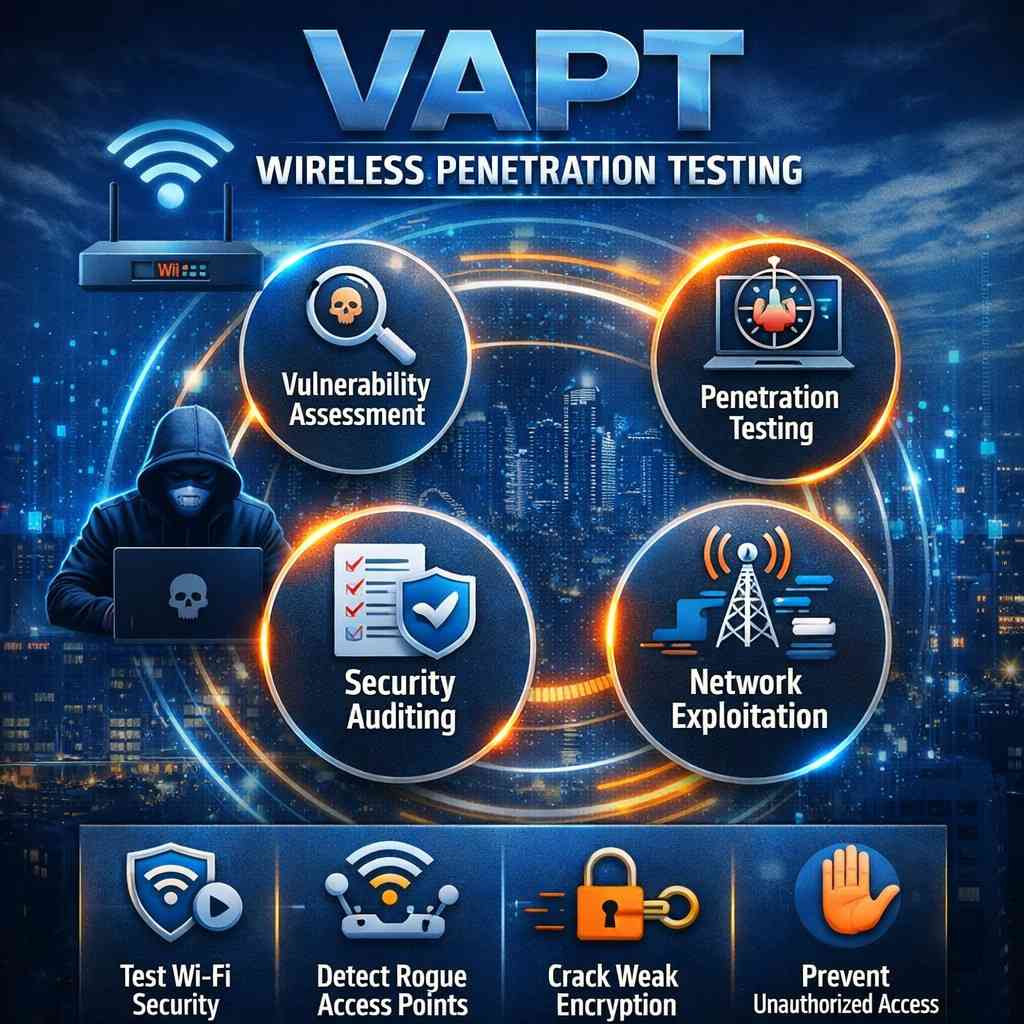
VAPT Wireless Penetration Testing
Wireless networks are an essential part of modern business operations, enabling seamless connectivity across offices, campuses, and remote environments. However, unlike wired networks, wireless communication operates over open air, making it highly susceptible to cyberattacks, unauthorized access, and data interception.
Wireless Penetration Testing (Wireless VAPT) is a specialized security assessment that evaluates the security of Wi-Fi networks and wireless infrastructure. It combines Vulnerability Assessment and Penetration Testing (VAPT) techniques to identify weaknesses and simulate real-world attacks on wireless networks.
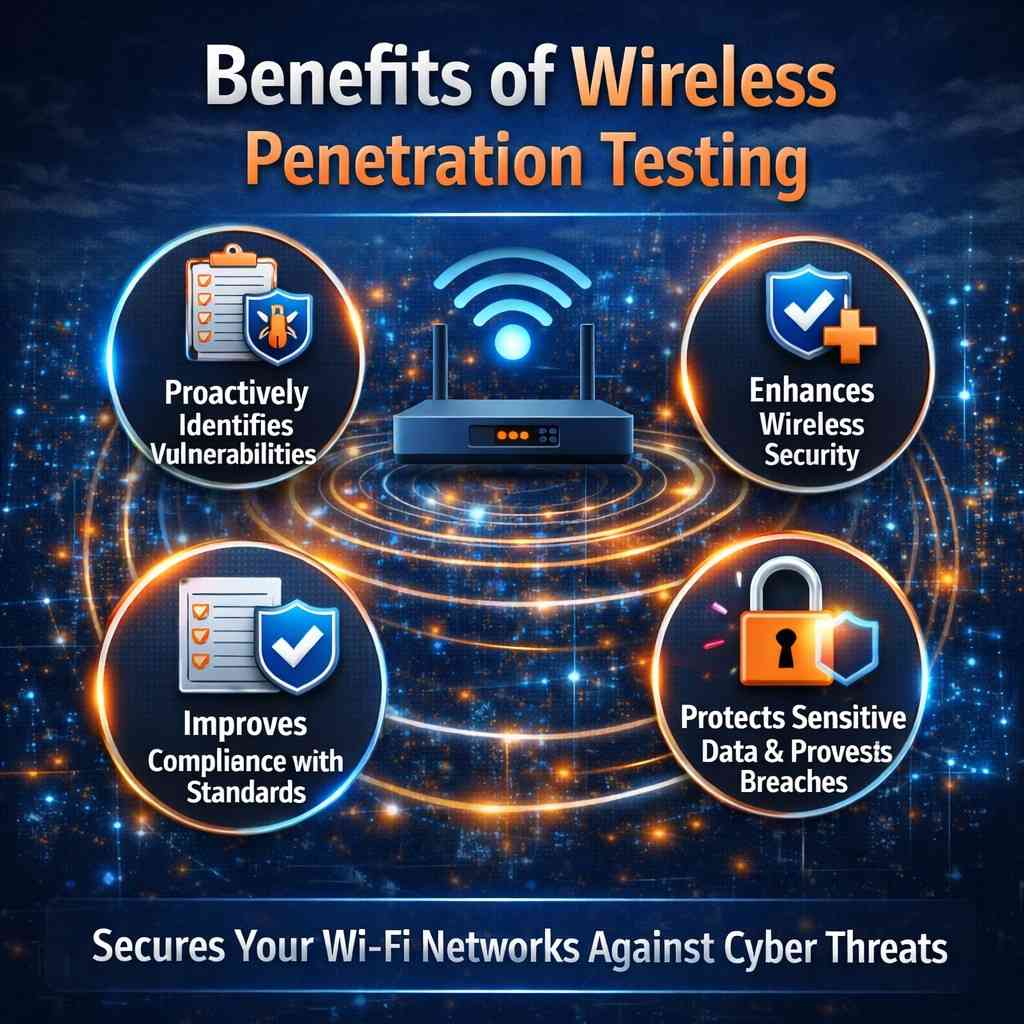
By proactively testing wireless environments, organizations can detect vulnerabilities and strengthen their defenses before attackers exploit them.